Chapter 83: Stack Memory Allocation and Management
Chapter Objectives
By the end of this chapter, you will be able to:
- Understand the architecture and purpose of the function call stack in a modern embedded Linux environment.
- Analyze the structure of a stack frame, including the roles of the stack pointer, frame pointer, return address, and local variables.
- Implement C programs that demonstrate stack memory allocation and trace their execution using the GNU Debugger (GDB).
- Diagnose and debug common stack-related issues, such as stack overflow, using system tools and programming techniques.
- Configure system limits and apply best practices to manage stack memory effectively in resource-constrained embedded applications.
- Explain the function prologue and epilogue sequences generated by a compiler and their role in managing the stack.
Introduction
In the intricate world of embedded Linux systems, memory is a finite and precious resource. While previous chapters may have explored the broad landscape of memory management, including virtual memory and the heap, this chapter drills down into one of the most fundamental and dynamic memory regions: the stack. The function call stack is the invisible mechanism that underpins the very structure of procedural programming. Every time a function is called, a new block of memory, known as a stack frame, is allocated. This frame holds the function’s local variables, arguments, and the crucial information needed to return to the caller. For an embedded developer, understanding the stack is not merely an academic exercise; it is a practical necessity.
The stack’s Last-In, First-Out (LIFO) nature makes it incredibly efficient for temporary data storage, but this efficiency comes with a critical limitation: its size is fixed and relatively small. On a powerful desktop computer, a stack overflow might be a rare and recoverable annoyance. On a headless embedded device, such as a Raspberry Pi 5 controlling a critical industrial process or collecting sensor data, a stack overflow can be a silent, catastrophic failure. An unterminated recursive function or an unexpectedly large local variable can exhaust the available stack space, corrupting adjacent memory and leading to unpredictable system behavior or a complete crash. This chapter will demystify the function call stack, transforming it from an abstract concept into a tangible, manageable component of your embedded system. We will explore its architecture on the ARMv8-A platform of the Raspberry Pi 5, learn to inspect it with professional debugging tools, and develop the skills to write robust, stack-aware code that is both efficient and reliable.
Technical Background
The journey of a program’s execution is a story of functions calling other functions. The function call stack is the data structure that the system uses to manage this intricate dance. It is a contiguous block of memory allocated for each thread when it is created. Its primary purpose is to keep track of the active functions, their local data, and the precise point to which each function should return control upon completion. This mechanism is elegant in its simplicity and speed, as allocating and deallocating memory is merely a matter of incrementing or decrementing a single processor register, the stack pointer.
The Architecture of the Stack
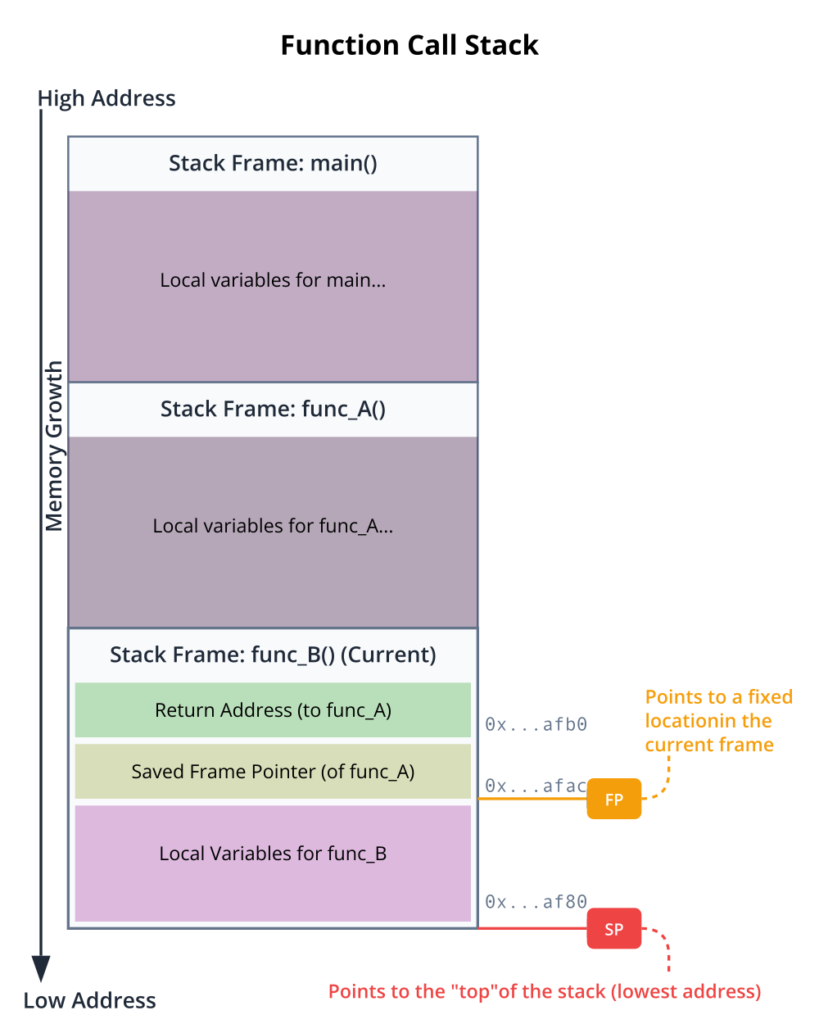
To truly grasp the stack’s operation, we must visualize it as a region of memory that grows and shrinks from one end. In most modern architectures, including the AArch64 architecture used by the Raspberry Pi 5, the stack grows downwards from a higher memory address to a lower one. The stack pointer (SP) is a special-purpose processor register that always holds the address of the “top” of the stack—which, confusingly, is the lowest memory address currently in use by the stack. When a function is called, the stack “grows” by decrementing the stack pointer, reserving space for the new function’s data. When the function returns, the stack “shrinks” by incrementing the stack pointer, effectively freeing that memory. This process is exceptionally fast compared to heap allocation, which involves more complex algorithms to find and manage free blocks of memory.
Each function call creates a new stack frame on the stack. A stack frame is a structured block of memory that contains all the necessary information for the execution of one function instance. While the exact layout can vary depending on the compiler, architecture, and optimization level, a typical stack frame contains several key components. It holds the arguments passed to the function, although modern calling conventions often pass the first several arguments in registers for efficiency. It also provides storage for all the function’s local variables—those declared within the function’s scope. Critically, it stores the return address, which is the memory address of the instruction in the calling function to which the program should return after the current function finishes.
To maintain a stable reference point within the shifting landscape of the stack, compilers often use another register: the frame pointer (FP), also known as the base pointer. The frame pointer holds an address within the current stack frame that remains constant throughout the function’s execution. Local variables and arguments can then be accessed at fixed, known offsets from the frame pointer. This provides a reliable way to access data, even as other data is pushed onto and popped off the top of the stack during nested function calls. The collection of all stack frames on the stack at any given moment represents the program’s call chain, with the most recently called function at the top.
The Function Prologue and Epilogue
The creation and destruction of a stack frame are not magic; they are the result of a standardized sequence of machine instructions meticulously inserted by the compiler at the beginning and end of every function. These sequences are known as the function prologue and function epilogue.
The function prologue is responsible for setting up the new stack frame. When a function is called, the prologue code executes first. Its primary jobs are to save the previous function’s frame pointer (so it can be restored later) and to establish the new frame pointer for the current function. A typical prologue on an AArch64 processor performs the following steps:
- It pushes the old frame pointer onto the stack to save it.
- It pushes the link register (LR), which holds the return address, onto the stack. The LR is a special register where the
BL(Branch with Link) instruction automatically stores the return address. - It sets the current frame pointer (FP) to the current stack pointer (SP) value, establishing the new frame’s base.
- It decrements the stack pointer further to allocate space for the function’s local variables.
Once the prologue is complete, the stack frame is fully formed, and the body of the function can execute. Local variables are accessed via their fixed offsets from the frame pointer.
Conversely, the function epilogue is the code that cleans up the stack frame just before the function returns. It precisely reverses the actions of the prologue to restore the stack and the processor state to what they were before the function was called. The epilogue performs these steps:
- It deallocates the space used by local variables by moving the stack pointer up to the location of the frame pointer.
- It pops the saved link register value from the stack back into the LR.
- It pops the saved frame pointer value from the stack back into the FP register, restoring the caller’s frame.
- Finally, it executes a return instruction (
RET), which jumps to the address stored in the link register, handing control back to the calling function.
This disciplined, symmetrical process of setup and teardown ensures that function calls can be nested to any depth (within the limits of the stack’s size) and that execution will always return correctly.
Tip: Compilers can perform an optimization called “frame pointer omission.” If a function has no complex local variable addressing, the compiler might decide not to use a frame pointer at all, accessing variables directly from the stack pointer. This frees up the FP register for general-purpose use but can make debugging more difficult, as the stable reference point within the stack frame is lost.
Stack Overflow: When Good Stacks Go Bad
The stack, for all its efficiency, has a finite size. The default stack size for a thread in Linux is typically a few megabytes (e.g., 8MB on many desktop systems), but it can be much smaller in embedded environments to conserve memory. A stack overflow occurs when a program attempts to use more stack space than is available. Because the stack and other memory segments (like the heap) reside in the same virtual address space, a stack that grows beyond its boundary will start overwriting adjacent memory. This is a severe and often fatal error.
The consequences of a stack overflow are unpredictable and dangerous. If the overwritten memory belongs to the heap, it can corrupt data structures in a way that causes a crash much later in the program’s execution, making the root cause incredibly difficult to trace. If the stack overwrites its own older frames, it can corrupt saved return addresses. When a function attempts to return, it will jump to a garbage address, almost certainly causing an immediate segmentation fault.
Two common programming errors are the primary culprits behind stack overflows. The first and most classic cause is infinite recursion. This happens when a recursive function lacks a proper base case (a condition to stop recurring) or the base case is never met. Each recursive call creates a new stack frame, and if the calls never stop, they will inevitably consume the entire stack.
The second common cause is the allocation of very large local variables. Declaring a large array or structure as a local variable places it directly on the stack. For example, a declaration like char buffer[2 * 1024 * 1024]; inside a function attempts to allocate 2MB on the stack. If the total available stack space is only 8MB, it doesn’t take many such allocations, perhaps combined with a deep call chain, to exhaust the available memory.
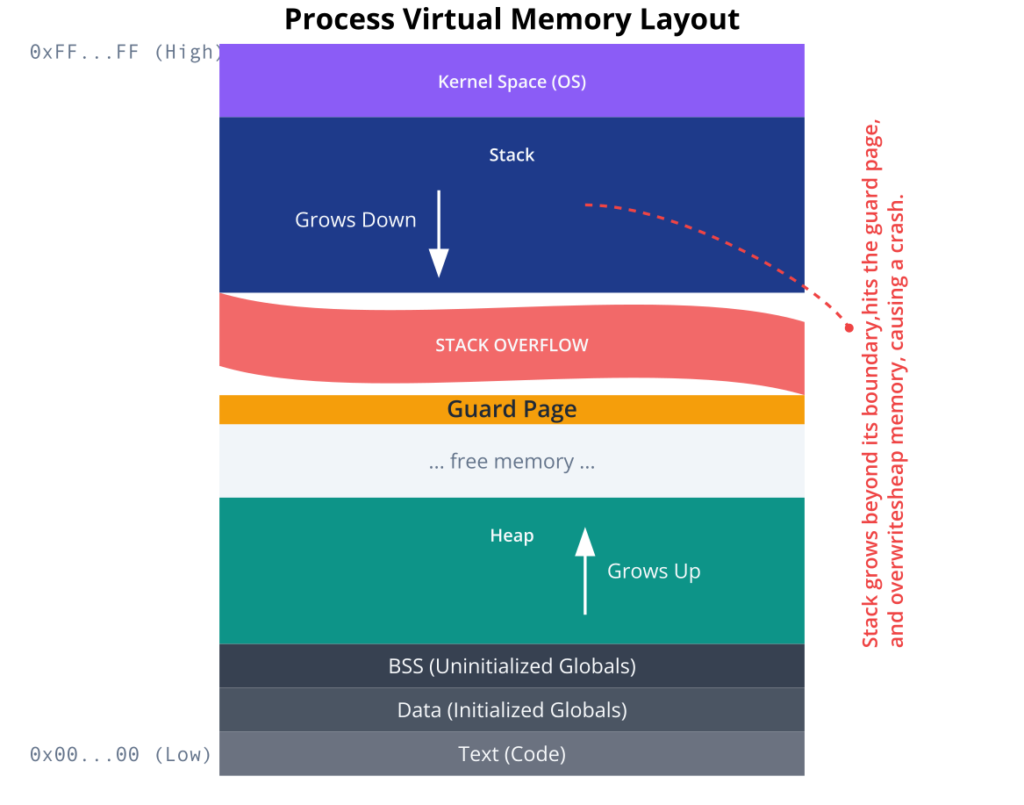
Detecting a stack overflow in an embedded system can be challenging. The system might simply hang, reboot, or behave erratically. The Linux kernel provides a protection mechanism called stack guard pages. A guard page is a special page of virtual memory placed just beyond the end of the stack’s allocated region. This page is marked as invalid in the page table. If the stack grows beyond its limit and touches the guard page, it triggers a page fault. The kernel’s page fault handler can then recognize this as a stack overflow, terminate the offending process with a segmentation fault, and log a message to the system log. This provides a clear and immediate indication of the problem, turning a silent data corruption bug into a loud, debuggable crash. Understanding and managing the stack is therefore a cornerstone of writing reliable embedded software.
Practical Examples
Theory provides the foundation, but true understanding comes from hands-on practice. In this section, we will use the Raspberry Pi 5 to explore the function call stack in a practical context. We will write C code, compile it using GCC, and use the GNU Debugger (GDB) to peer inside the machine and observe the stack directly.
Warning: Ensure your Raspberry Pi 5 is running a recent version of Raspberry Pi OS (or another suitable Linux distribution). All commands should be run in the terminal. You will need the
build-essentialpackage installed (sudo apt-get install build-essential) to get the GCC compiler and related tools.
Example 1: A Simple Function Call and Stack Inspection
Our first goal is to visualize a simple stack frame. We will write a program with a main function that calls another function. We will then use GDB to set a breakpoint and inspect the state of the registers and memory.
Code Snippet
Create a file named stack_simple.c with the following content:
#include <stdio.h>
// A simple function to demonstrate a stack frame.
// It takes two integer arguments and has one local variable.
int add_numbers(int a, int b) {
int result = 0; // A local variable
result = a + b;
return result; // The return value is typically passed back in a register (x0).
}
int main() {
int x = 10;
int y = 20;
int z = 0;
z = add_numbers(x, y);
printf("The result is: %d\n", z);
return 0;
}
Build and Debug Steps
1. Compile with Debug Symbols: To make our program debuggable with GDB, we must compile it with the -g flag. This flag tells GCC to include extra information in the executable file that maps the machine code back to the original source code lines, variable names, and function names. We also use -O0 to disable optimizations, which prevents the compiler from reordering code or optimizing away the frame pointer, making the stack easier to follow.
gcc -g -O0 -o stack_simple stack_simple.c
2. Start GDB: Launch the debugger and load our compiled program.
gdb ./stack_simple3. Set a Breakpoint: We want to pause execution inside the add_numbers function to inspect its stack frame. We’ll set a breakpoint at the line where result is calculated.
(gdb) break add_numbers
Breakpoint 1 at 0x59c: file stack_simple.c, line 6.4. Run the Program: Start the program execution under GDB’s control. It will run until it hits our breakpoint.
(gdb) run
Starting program: /home/pi/stack_simple
Breakpoint 1, add_numbers (a=10, b=20) at stack_simple.c:6
6 int result = 0; // A local variable5. Inspect the Stack: Now that we are paused inside add_numbers, we can use GDB commands to examine the stack.
– Backtrace: The bt (or backtrace) command shows the entire function call chain.
(gdb) bt
#0 add_numbers (a=10, b=20) at stack_simple.c:6
#1 0x00000000000006e0 in main () at stack_simple.c:15#0 (add_numbers), which was called by frame #1 (main).
– Examine Registers: Let’s look at the key registers: sp (stack pointer), fp (frame pointer), and lr (link register). The AArch64 architecture uses x29 for the frame pointer and x30 for the link register.
(gdb) info registers sp fp lr
sp 0x7ffffff0d0 0x7ffffff0d0
fp 0x7ffffff0e0 0x7ffffff0e0
lr 0x6e0 main+444fp address (0x...0e0) is higher than the sp address (0x...0d0), confirming the stack grows downwards. The lr holds the address within main to which we will return.
– Inspect the Stack Frame: We can view the memory content of the stack frame. Let’s examine the memory between the frame pointer and the stack pointer. The command x/4wg means “examine 4 words of memory in giant-word (64-bit) format, printing in hex.”
(gdb) x/4wg $fp-16
0x7ffffff0d0: 0x0000000000000000 0x0000000000000000
0x7ffffff0e0: 0x0000007ffffff1f0 0x00000000000006e00x...0e0 is our frame pointer ($fp). At this address, we see two 64-bit values. The first (0x...f1f0) is the saved frame pointer of the caller (main). The second (0x...06e0) is the saved link register—the return address, which matches the lr value we saw earlier. The two 64-bit words below the frame pointer (at 0x...0d0 and 0x...0d8) are the space allocated for our local variable result. This is a direct view of the stack frame structure we discussed in the theory section.
Example 2: Triggering and Analyzing a Stack Overflow
Now, let’s write a program that intentionally causes a stack overflow through uncontrolled recursion. This will demonstrate how such an error manifests and how the system reports it.
Code Snippet
Create a file named stack_overflow.c.
staBuild and Run Steps
1. Compile the Program: No debug symbols are needed this time; we just want to observe the crash.
gcc -o stack_overflow stack_overflow.c2. Check Stack Size Limit: Before running, let’s check the current stack size limit for our shell session using the ulimit command.
ulimit -s 8192
3. Run the Program: Execute the program and observe the output.
./stack_overflow
Call number: 8125, stack pointer at: 0x7fff72d8e4b0
Call number: 8126, stack pointer at: 0x7fff72d8e0b0
Call number: 8127, stack pointer at: 0x7fff72d8dcb0
Segmentation faultrecursive_function allocates 1KB (buffer) plus some overhead for the stack frame. After about 8000 calls, it has consumed the entire 8MB of available stack space, hit the guard page, and the kernel has terminated it.
4. Analyze with dmesg: The kernel logs important system events. We can check the kernel message buffer with the dmesg command to see if it recorded anything about our crash.
dmesg | tail
[ 1234.567890] stack_overflow[9876]: segfault at 7fff72d8bfff ip 000000000040061c sp 0000007fff72d8c000 error 6 in stack_overflow[400000+1000]
stack_overflow (with process ID 9876) caused a segmentation fault. It records the instruction pointer (ip) and the stack pointer (sp) at the time of the fault, confirming a stack-related error. This is the result of the stack guard page doing its job.
Example 3: Mitigating Stack Overflow
The most common way to fix stack-related overflow issues caused by large data structures is to move them from the stack to the heap. The heap is a much larger region of memory designed for dynamic, long-term allocation.
Code Snippet
Let’s modify our large local variable example. Create a file named heap_alloc.c.
#include <stdio.h>
#include <stdlib.h> // Required for malloc and free
#define BUFFER_SIZE (2 * 1024 * 1024) // 2MB
void process_data() {
// Allocate the buffer on the heap instead of the stack
char *buffer = (char *)malloc(BUFFER_SIZE);
if (buffer == NULL) {
perror("Failed to allocate memory on the heap");
return;
}
printf("Successfully allocated 2MB buffer on the heap at address: %p\n", buffer);
// ... do some work with the buffer ...
buffer[0] = 'H';
buffer[1] = 'i';
buffer[2] = '\0';
printf("Buffer content: %s\n", buffer);
// IMPORTANT: Free the memory when done
free(buffer);
printf("Heap memory freed.\n");
}
int main() {
process_data();
return 0;
}
Analysis
In this revised version, the large 2MB buffer is no longer a local variable. Instead, malloc() is used to request that memory from the heap. The process_data function’s stack frame is now tiny, containing only the pointer buffer itself (typically 8 bytes on a 64-bit system), not the 2MB of data it points to. This approach completely avoids the risk of stack overflow from this allocation.
Tip: The trade-off is that heap allocation is slower than stack allocation and requires careful manual management. You must always
free()the memory youmalloc(), or you will create a memory leak, where the heap memory is consumed and never returned to the system. In a long-running embedded application, memory leaks are just as dangerous as stack overflows.
Common Mistakes & Troubleshooting
Even with a solid theoretical understanding, developers often encounter a set of common pitfalls when dealing with stack memory. Recognizing these patterns early is key to efficient debugging and building robust systems.
flowchart TD
A[Start: Segmentation Fault Occurs] --> B{Is it reproducible?};
style A fill:#ef4444,stroke:#ef4444,stroke-width:2px,color:#ffffff
B -- No --> C[Add extensive logging.<br>Analyze core dumps if available.<br>Look for race conditions or memory corruption.];
style B fill:#f59e0b,stroke:#f59e0b,stroke-width:1px,color:#ffffff
B -- Yes --> D[Compile with debug symbols <b>-g -O0</b>];
style D fill:#0d9488,stroke:#0d9488,stroke-width:1px,color:#ffffff
D --> E[Run program in GDB];
style E fill:#0d9488,stroke:#0d9488,stroke-width:1px,color:#ffffff
E --> F{Program crashes in GDB};
style F fill:#f59e0b,stroke:#f59e0b,stroke-width:1px,color:#ffffff
F --> G["Use <b>'bt'</b> (backtrace) command<br>to view the call stack"];
style G fill:#0d9488,stroke:#0d9488,stroke-width:1px,color:#ffffff
G --> H{What does the backtrace show?};
style H fill:#f59e0b,stroke:#f59e0b,stroke-width:1px,color:#ffffff
H -- "Thousands of identical calls" --> I["<b>Diagnosis:</b><br>Infinite Recursion<br>(Stack Overflow)"];
style I fill:#8b5cf6,stroke:#8b5cf6,stroke-width:1px,color:#ffffff
I --> J[Fix the base case in<br>the recursive function.];
style J fill:#10b981,stroke:#10b981,stroke-width:2px,color:#ffffff
H -- "Crash in a library function<br>like strcpy(), gets()" --> K[<b>Diagnosis:</b><br>Buffer Overflow<br>corrupting stack];
style K fill:#8b5cf6,stroke:#8b5cf6,stroke-width:1px,color:#ffffff
K --> L["Replace with safe alternatives<br>(strncpy(), fgets())."];
style L fill:#10b981,stroke:#10b981,stroke-width:2px,color:#ffffff
H -- "Crash on a memory access<br>e.g., mov [reg], val" --> M[Inspect the source code at the<br>crash location. Check pointers<br>and array indices.];
style M fill:#0d9488,stroke:#0d9488,stroke-width:1px,color:#ffffff
M --> N{Is a pointer NULL or invalid?};
style N fill:#f59e0b,stroke:#f59e0b,stroke-width:1px,color:#ffffff
N -- Yes --> O[<b>Diagnosis:</b><br>NULL Pointer Dereference or<br>use of uninitialized pointer.];
style O fill:#8b5cf6,stroke:#8b5cf6,stroke-width:1px,color:#ffffff
O --> P[Add checks for NULL<br>before using pointers.];
style P fill:#10b981,stroke:#10b981,stroke-width:2px,color:#ffffff
N -- No --> Q["Check 'dmesg' for kernel logs.<br>Look for messages related to<br>stack guard page faults."];
style Q fill:#eab308,stroke:#eab308,stroke-width:1px,color:#1f2937
Q --> R[<b>Diagnosis:</b><br>Stack overflow from large<br>local variables.];
style R fill:#8b5cf6,stroke:#8b5cf6,stroke-width:1px,color:#ffffff
R --> S["Move large variables<br>from the stack to the heap<br>using malloc()."];
style S fill:#10b981,stroke:#10b981,stroke-width:2px,color:#ffffff
Exercises
These exercises are designed to reinforce the concepts of stack management and debugging on your Raspberry Pi 5.
- Exercise 1: Manual Stack Frame Analysis
- Objective: To manually calculate and verify the offsets of local variables from the frame pointer.
- Steps:
- Modify the
stack_simple.cprogram. Add two more local variables of different types (e.g.,char c;andlong long d;) to theadd_numbersfunction. - Compile with
-gand-O0. - Run it in GDB and break inside
add_numbersafter the local variables are initialized. - Print the addresses of all local variables (
p &variable_name). - Print the value of the frame pointer (
info reg fp). - Calculate the offset of each local variable from the frame pointer (e.g.,
address_of_variable - address_in_fp). - Verify that you can access the variable’s content using the
xcommand in GDB with the frame pointer and your calculated offset (e.g.,x/d $fp - offset). This exercise builds a concrete mental model of the stack frame layout.
- Modify the
- Exercise 2: Setting Stack Size and Observing Limits
- Objective: To understand how to control and observe the effects of stack size limits.
- Steps:
- Use the
stack_overflow.cprogram from the examples. - Use the
ulimit -s <kilobytes>command to drastically reduce the allowed stack size (e.g.,ulimit -s 256for 256 KB). - Run the
./stack_overflowprogram again. - Observe: How many recursive calls does it take to crash now? The number should be significantly lower.
- Restore the stack limit to a higher value (e.g.,
ulimit -s 8192). - Verification: This demonstrates the direct relationship between the
ulimitsetting and the program’s available stack resources.
- Use the
- Exercise 3: Fixing a Bug with a Corrupted Stack
- Objective: To debug a real-world scenario where a buffer overflow corrupts a local variable on the stack.
- Steps:
- Create a new C file with the following code:
#include <stdio.h> #include <string.h> void process_input() { int authenticated = 0; char input_buffer[16]; printf("Enter password: "); gets(input_buffer); // Intentionally use the unsafe gets() if (authenticated) { printf("Access Granted!\n"); } else { printf("Access Denied.\n"); } } int main() { process_input(); return 0; } - Compile and run the program. If you enter a short password (e.g., “hello”), it will correctly print “Access Denied.”
- Now, run it again and enter a very long string of characters (e.g., 30 ‘A’s). Observe that it prints “Access Granted!”
- Analyze: Use GDB to step through the
process_inputfunction. Set a watchpoint on theauthenticatedvariable (watch authenticated). Observe how thegets()function, when given too much input, writes past the end ofinput_bufferand overwrites the memory location ofauthenticated, changing its value from 0 to non-zero. - Fix: Replace the
gets(input_buffer);line withfgets(input_buffer, sizeof(input_buffer), stdin);and re-test to confirm the bug is fixed.
- Create a new C file with the following code:
Summary
This chapter provided a deep dive into the function call stack, a critical component of program execution in Embedded Linux. By understanding its mechanics, you gain the ability to write more efficient, reliable, and secure code.
- Key Concepts Recap:
- The call stack is a LIFO data structure that manages active function calls. It grows downwards in memory on AArch64 systems.
- Each function call creates a stack frame, which holds local variables, function arguments, and the return address.
- The stack pointer (SP) and frame pointer (FP) are key registers used to manage the stack.
- Function prologues and epilogues are compiler-generated code sequences that create and destroy stack frames.
- Stack overflow is a critical error caused by exhausting stack memory, typically through infinite recursion or large local variables.
- Using the heap (
malloc) for large data structures is the standard way to prevent stack overflow. - Tools like GDB,
ulimit, anddmesgare essential for debugging stack-related issues on a Linux system.
By completing the examples and exercises, you have moved from theory to practice, gaining tangible skills in stack analysis and troubleshooting on the Raspberry Pi 5. This knowledge is not just academic; it is fundamental to professional embedded systems development.
Further Reading
- ARM Architecture Reference Manual for ARMv8-A: The definitive source for the AArch64 architecture, including details on the procedure call standard and register usage. Available from the ARM Developer website.
- System V Application Binary Interface (ABI) – AArch64 Supplement: This document specifies the low-level details of the function call convention, including how stack frames are laid out and how arguments are passed.
- GDB Documentation: The official GNU Debugger manual is an invaluable resource for mastering its powerful features for inspecting program state. (https://www.gnu.org/software/gdb/documentation/)
- “What Every Programmer Should Know About Memory” by Ulrich Drepper: An exhaustive paper covering many aspects of computer memory, including a detailed look at the stack and heap. While dense, it is a classic text for systems programmers.
- Linux Kernel Documentation – Memory Management: For those wishing to go deeper, the kernel documentation provides insights into how the operating system manages memory for processes, including the setup of the initial stack. (https://www.kernel.org/doc/html/latest/admin-guide/mm/index.html)
- “Hacking: The Art of Exploitation, 2nd Edition” by Jon Erickson: While focused on security, this book gives one of the clearest explanations of how the stack works and how buffer overflows can be used to exploit programs, providing a powerful incentive to write stack-safe code.

